Решение пасхалки из анонса CTF от BI.ZONE
За несколько недель до старта регистрации на CTF, организованный компанией BI.ZONE, на различных информационных порталах был выложен анонс этого мероприятия.
Если посмотреть на анонс, например на сайте ZN2016, то можно заметить некоторую странность в форматировании текста.
Опытный глаз заметит, что слова разделяются одним или двумя пробелами. Это наводит на мысль, что в сообщении закодирована информация.
Есть много кодов, способных шифровать информацию таким образом, но подходит только один: один пробел кодирует 0, два — 1. После декодирования можно было получить бинарную строку:
0111000001110010011011110110110101101111001011100110
0010011010010010111001111010011011110110111001100101
После перевода в ASCII получится promo.bi.zone. Этим заканчивается первый этап задания.
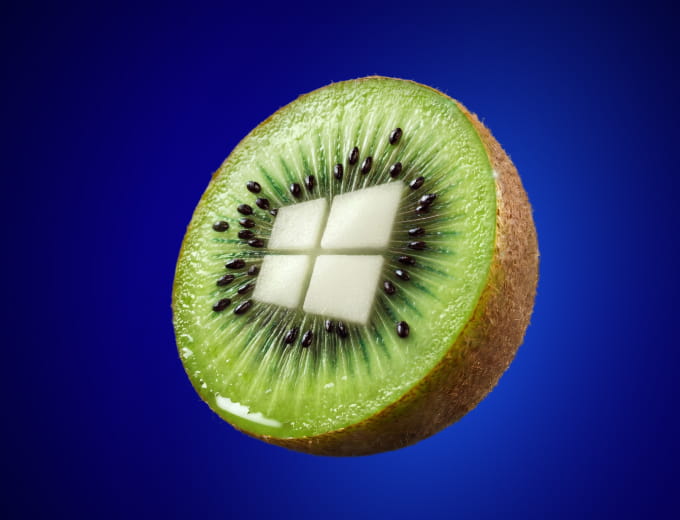
При переходе на сайт выяснялось, что он недоступен. При дальнейшем исследовании, например nmap’ом, можно было увидеть, что на сервере открыты два порта — 22 (SSH) и 90. На 90-м порту размещена большая картинка с логотипом BI.ZONE.
Рассмотрев ее внимательно, можно увидеть QR код внизу картинки. Этот код содержит текст Try to find me(; Father calls me ctfzone. Очевидно, что нужно найти кого-то с таким ником в одном из популярных сервисов.
Фраза Father calls me является отсылкой к боту в Telegram, который регистрирует ботов, BotFather. В Telegram можно найти бота с ником @ctfzone.
При старте общения с ботом вы узнаете, что вам нужно решить несколько судоку. Судоку решаются любым способом, например с помощью модуля pythonsudoku. После решения десяти судоку бот отвечает сообщением: Post your flag on twitter with #ctfzone and mention @CtfZone: flag.
Опубликовав соответствующий твит, можно было получить свой приз.
Тот, кто первым решил все задания, получил инвайт на ZN2016, остальные же получат свои призы на конференции.